When designing how the Colorado All Payer Claims Database (CO APCD) was to be built and administered, protecting health information was the highest priority. Colorado statute CRS 25.5-1-204 requires the CO APCD to “[p]rotect patient privacy in compliance with state and federal medical privacy laws while preserving the ability to analyze data and share with providers and payers to ensure accuracy prior to the public release of information[.]” This ensures that all aspects of CO APCD data collection, processing, storage, and analysis complies with the Health Insurance Portability and Accountability Act (HIPAA) privacy and security requirements as well as all others at the state and federal levels.
Several measures and processes ensure that CIVHC and data managers, the Human Services Research Institute (HSRI) and NORC at the University of Chicago, adhere to the highest standards of security and confidentiality. These include:
- overlapping types of security provisions that constantly protect CO APCD data files;
- reinforcing layers of security which are multiple electronic firewalls;
- controlled access to the physical plant;
- granting permissions to access a secure website to submit files; and
- emphasizing privacy and security at every point in the data transfer, storage, and analysis processes.
Data Submission and Storage
When health insurance payers submit files to the CO APCD, the data sets are always encrypted and sent to the CO APCD data management vendor over a secure connection unique to each submitter.
All CO APCD data is stored in a secure section of the NORC Data Enclave®, a protected platform where only authorized users may access data and tools to conduct analyses. Access is granted via role-based permissions which apply to both file storage and database systems in the Data Enclave. The file and database storage provisioned for CIVHC within the Data Enclave uses physical media that are encrypted at rest.
The NORC Data Enclave® secure infrastructure is an isolated network, which enhances the confidentiality and integrity of transmitted and stored data. All network and telecommunication equipment is housed in locked facilities. Datacenter operations, including CO APCD infrastructure, are maintained at a SOC 2 Type II compliant facility offsite from the data manager that is audited on an annual basis.
CO APCD data managers require internal network data storage services to store all project-related data files. Partitioned network storage is provided for each project to mitigate the potential for data loss due to accidents, computer equipment malfunction, corruption, unauthorized security breaches, or human error, and to administer access rights regarding privacy issues related to both legal and contractual obligations. Additionally, a wide array of network security precautions are undertaken to ensure the proper storage of all project data.
Encryption
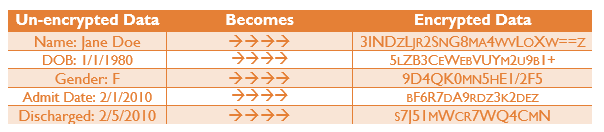
Data encryption techniques offer additional protection. All CO APCD data is encrypted both while in motion (or being transmitted) and at rest (while stored). This methodology is used throughout the CO APCD. An example of encryption is as follows:
De-identification: Protected data elements such as name, street address and Social Security Number are removed as part of initial processing and replaced with a unique member identification number. Depending upon the type of data requested, birth date is replaced with age or age range, and zip code data is aggregated to the first three digits. Data suppression rules are in place to prevent the release of any information that may make it possible to identify any individual represented in the CO APCD database.